Why Every Company in Dubai Needs Advanced Endpoint Security
If you are looking to protect your business from modern cyber threats, implementing advanced endpoint security is essential. Companies rely heavily on computers, laptops, smartphones, and other connected devices to perform daily operations. Each of these devices represents an endpoint within the company’s network. If one endpoint becomes compromised, attackers may gain access to the entire system, potentially leading to data breaches, operational disruptions, and financial losses.
Businesses in Dubai operate in a highly digital environment where employees frequently access company systems through multiple devices. While this improves flexibility and productivity, it also increases cybersecurity risks. Cybercriminals often target endpoints because they can be easier to exploit compared to centralized servers.
Technology providers such as Atop Computer Solution LLC help businesses implement advanced endpoint security solutions that protect devices, monitor threats, and secure sensitive business data. With the right endpoint protection strategy, organizations can safeguard their IT infrastructure and maintain a secure digital workplace.
Understanding Endpoint Security
Endpoint security refers to the protection of devices that connect to a company’s network. These devices include desktop computers, laptops, mobile phones, tablets, and servers. Since employees frequently access corporate systems through these devices, endpoints become potential entry points for cyber attacks.
Endpoint security solutions monitor and protect these devices by detecting suspicious activities, blocking malware, and enforcing security policies. They ensure that every device connected to the network follows strict security standards.
Modern endpoint security platforms go beyond traditional antivirus software. They use advanced technologies such as behavioral analysis, artificial intelligence, and real-time monitoring to detect emerging threats before they cause damage.
Organizations that invest in advanced endpoint protection create a stronger defense against cyber attacks that target individual devices.
Are you searching for an It Amc Dubai UAE? Connect to Atop Computer Solution LLC.
Why Endpoint Security Is Critical for Businesses
Businesses store valuable data including financial records, customer information, intellectual property, and internal communications. If attackers gain access to a single device, they may be able to move through the network and access sensitive information.
Endpoint security protects businesses from these risks by monitoring device activity and preventing unauthorized access.
Another reason endpoint security is essential is the growing number of remote and mobile workers. Employees often access company systems from different locations, which increases the number of devices connected to the network. Without proper security measures, these devices can become vulnerable to cyber threats.
Implementing advanced endpoint protection helps organizations maintain secure digital environments and prevent unauthorized system access.
Protecting Devices from Malware and Ransomware
One of the primary purposes of endpoint security is to protect devices from malware and ransomware attacks.
Malware Detection and Prevention
Malware refers to malicious software designed to damage systems or steal sensitive information. It can enter a device through infected files, malicious email attachments, or unsafe websites.
Endpoint security tools scan files, applications, and system activity to detect malicious software. When suspicious activity is identified, the system automatically blocks or removes the threat.
Advanced detection technologies can identify previously unknown malware based on unusual behavior patterns.
Ransomware Protection
Ransomware attacks involve malicious software that locks access to files or systems until a ransom payment is made. These attacks can cause severe disruption to business operations.
Endpoint protection solutions monitor system activity and detect suspicious file encryption attempts. When ransomware behavior is detected, the system stops the process and isolates the affected device.
Companies implementing endpoint security through Atop Computer Solution LLC can protect their devices from these dangerous cyber threats.
Are you searching for a Buy Microsoft Office 365 in UAE? Connect to Atop Computer Solution LLC.
Securing Remote and Mobile Workforces
Remote work has become common in many organizations. Employees often work from home, travel frequently, or access company systems through mobile devices.
While remote access improves flexibility, it also creates security challenges.
Secure Device Access
Endpoint security ensures that only authorized devices can connect to company systems. Devices must meet security requirements such as updated operating systems and installed security software.
This prevents compromised or unauthorized devices from accessing sensitive business data.
Protection Outside the Office Network
Employees using public networks or home internet connections may face additional cyber risks. Endpoint security solutions protect devices even when they are not connected to the corporate network.
This ensures that employees remain protected regardless of their working location.
Real-Time Threat Monitoring
Modern endpoint security platforms include real-time monitoring tools that continuously analyze device activity. These tools detect suspicious behavior and respond quickly to potential threats.
Behavioral Analysis
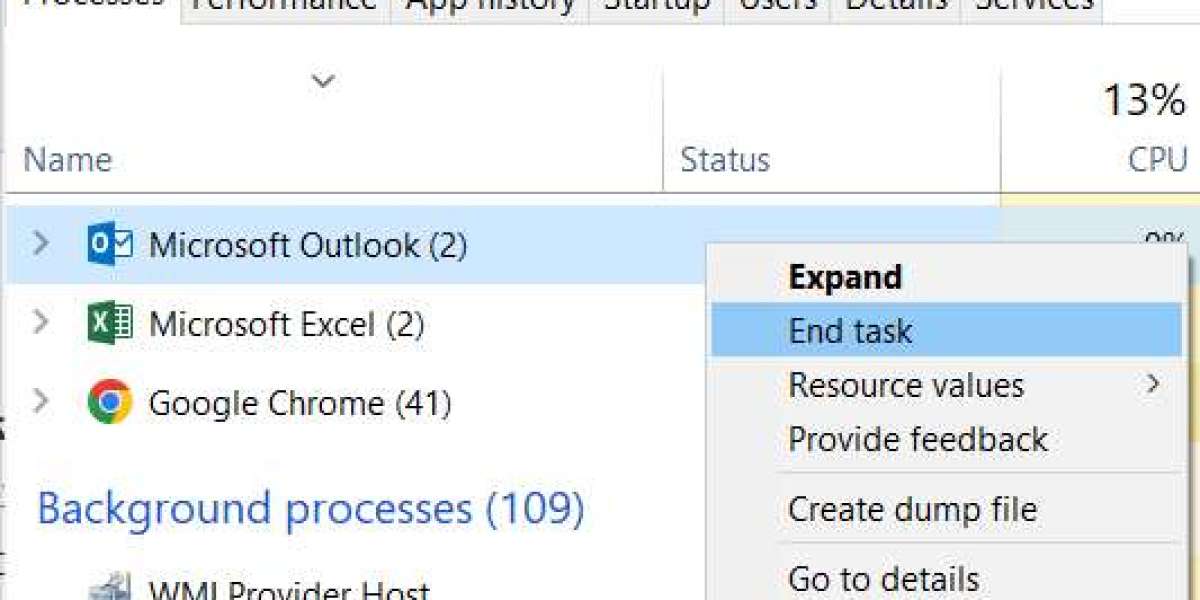
Instead of relying solely on known virus signatures, advanced endpoint protection systems analyze device behavior. If an application begins performing unusual actions, such as accessing restricted files or modifying system settings, the security system investigates the activity.
Behavioral analysis allows organizations to detect new threats that traditional antivirus software might miss.
Automated Threat Response
When suspicious activity is detected, endpoint security solutions can automatically isolate affected devices to prevent threats from spreading across the network.
Automated responses help organizations contain cyber incidents quickly and minimize damage.
Businesses working with Atop Computer Solution LLC can implement monitoring systems that provide complete visibility into endpoint security activity.
Preventing Data Breaches
Data breaches occur when unauthorized individuals gain access to confidential business information. These incidents can cause financial losses, legal issues, and reputational damage.
Endpoint security helps prevent data breaches by controlling how devices access and transfer sensitive information.
Data Encryption
Many endpoint security platforms include encryption features that protect stored data. Even if a device is stolen or lost, encrypted data cannot be accessed without proper authorization.
Encryption ensures that confidential information remains protected.
Access Control and Authentication
Endpoint protection systems also enforce strong authentication measures. Users must verify their identity before accessing sensitive data or applications.
Multi-factor authentication and role-based access controls prevent unauthorized individuals from accessing critical systems.
Are you searching for Apple Products? Connect to Atop Computer Solution LLC.
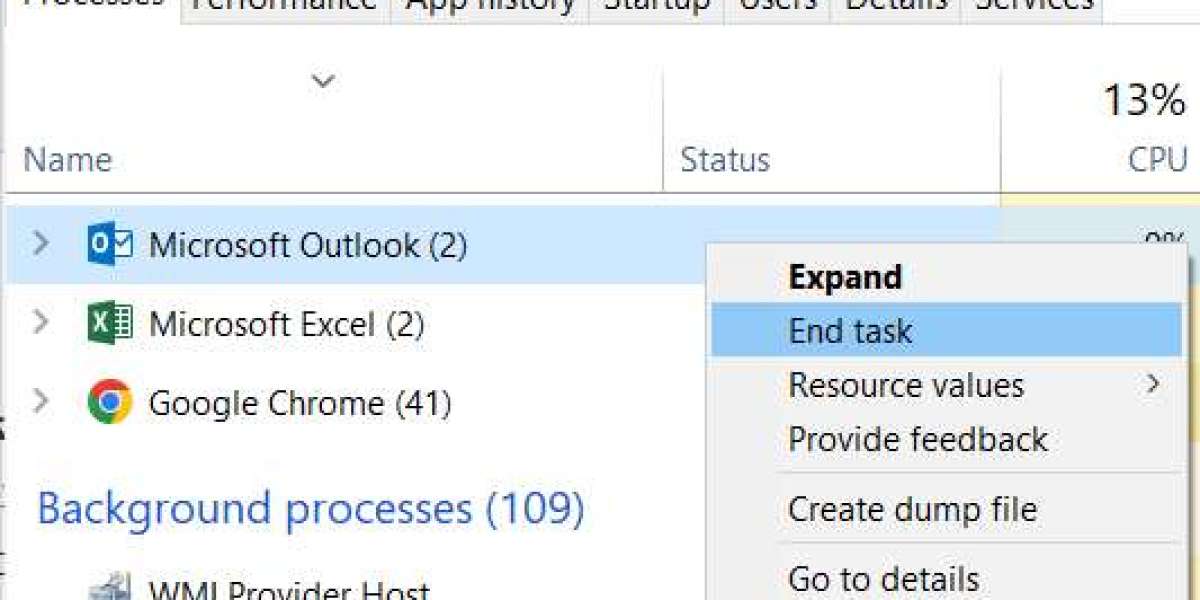
Managing Devices Across the Organization
Large organizations often manage hundreds or even thousands of devices connected to their networks. Endpoint security platforms provide centralized management tools that allow administrators to monitor and control all devices from a single dashboard.
Centralized Security Management
Administrators can configure security policies, install updates, and monitor device activity across the organization. This centralized approach simplifies IT management and ensures consistent security standards.
Automated Security Updates
Keeping devices updated is essential for preventing cyber attacks. Endpoint security systems automatically distribute updates and security patches to connected devices.
Regular updates protect systems from newly discovered vulnerabilities.
Companies partnering with Atop Computer Solution LLC can implement centralized endpoint management systems that improve visibility and security control.
Supporting Regulatory Compliance
Many industries must follow strict data protection regulations to safeguard sensitive information. Businesses that fail to protect data may face legal penalties and regulatory violations.
Endpoint security solutions help organizations comply with these regulations by implementing secure data storage, access controls, and monitoring systems.
Compliance with cybersecurity standards also demonstrates a company’s commitment to protecting customer data and maintaining responsible business practices.
Organizations operating in regulated sectors particularly benefit from strong endpoint security frameworks.
Partnering with Cybersecurity Experts
Implementing effective endpoint security requires expertise and continuous monitoring. Many businesses choose to work with professional IT service providers to strengthen their cybersecurity strategies.
Technology providers such as Atop Computer Solution LLC offer advanced endpoint protection solutions, threat monitoring services, and cybersecurity consulting for organizations in Dubai.
Professional support ensures that endpoint security systems are properly configured, maintained, and updated to protect against evolving cyber threats.
Working with experienced cybersecurity experts allows businesses to focus on their operations while maintaining strong digital security.
If you are searching for IT Support Services in Dubai UAE? Connect to Atop Computer Solution LLC.
Conclusion
Advanced endpoint security is essential for businesses that rely on connected devices and digital systems. Each device connected to a company’s network represents a potential entry point for cyber attackers. Without proper protection, a single compromised device can lead to serious security breaches.
Endpoint security solutions protect devices from malware, ransomware, and unauthorized access while providing real-time monitoring and automated threat responses. These technologies help businesses safeguard sensitive data and maintain secure IT environments.
Organisations in Dubai that invest in advanced endpoint protection are better prepared to defend against evolving cyber threats and protect their digital assets.
By partnering with trusted IT providers like Atop Computer Solution LLC, businesses can implement reliable endpoint security strategies that protect their devices, networks, and valuable business information.
Google Map - https://share.google/KSpp3DAFljvpkzZNo
Follow these links for more information:
https://www.acs-dxb.com/services/it-support-services-in-dubai-uae
https://www.acs-dxb.com/services/it-amc-dubai-uae
https://www.acs-dxb.com/products/apple