Attackers now use automation, generative AI, and adaptive malware to exploit vulnerabilities faster than traditional security systems can respond. Static firewalls and rule-based detection engines are no longer sufficient.
The modern enterprise must evolve from passive defense to active cyber resilience. That shift is being driven by advanced AI development Services that enable systems to detect, respond, and adapt autonomously. At the same time, the rapid expansion of connected devices means that every IoT endpoint can become a potential attack surface—making collaboration with a secure-by-design IoT App development company more critical than ever.
The future of cybersecurity is not just protection. It is self-defense powered by intelligence.
From Perimeter Security to Intelligent Defense
The perimeter model assumed that threats came from outside the network. In today’s distributed cloud and IoT ecosystems, that assumption is outdated.
Modern digital infrastructures include:
Multi-cloud environments
Remote workforces
Edge devices
Third-party API integrations
Autonomous systems
This complexity requires AI systems capable of continuously analyzing behavior across networks, users, and devices.
Organizations leveraging AI development Services are deploying behavioral analytics engines that identify anomalies in real time—detecting threats based on deviations rather than predefined signatures.
AI-Driven Threat Detection: Moving Beyond Signatures
Traditional cybersecurity tools relied heavily on known attack signatures. The problem? Zero-day vulnerabilities and AI-generated malware evolve too quickly.
AI-powered systems now use:
Machine learning anomaly detection
Real-time traffic pattern analysis
Behavioral biometrics
Deep packet inspection powered by neural networks
Instead of waiting for known threat indicators, these systems flag unusual behavior patterns immediately.
For example, if an IoT device suddenly begins transmitting data outside normal operational hours, AI systems can quarantine it automatically.
This is where integration between AI development Services and an experienced IoT App development company becomes vital. Connected ecosystems must be designed with embedded intelligence capable of autonomous defense.
Self-Healing Systems and Autonomous Response
Detection is only the first step. In 2026, cyber resilience depends on autonomous response mechanisms.
Advanced AI systems can:
Isolate compromised devices
Revoke suspicious credentials
Trigger backup restoration
Reroute network traffic
Patch vulnerabilities automatically
Self-healing architectures reduce downtime and minimize damage.
Organizations that embed AI development Services into their security infrastructure move from reactive incident response to proactive containment strategies.
IoT Security in a Hyper-Connected World
The proliferation of IoT devices introduces significant cybersecurity risks. Many connected devices lack robust built-in protections, making them attractive entry points for attackers.
A forward-thinking IoT App development company now implements:
Secure boot processes
Encrypted device-to-cloud communication
Certificate-based authentication
Remote firmware updates
Device behavior monitoring
When combined with AI-powered anomaly detection, these measures create layered security architectures that adapt dynamically to emerging threats.
As smart factories, connected vehicles, and intelligent buildings expand, IoT security is no longer optional—it is foundational.
AI vs. AI: The New Cyber Battlefield
One of the defining trends of 2026 is the rise of AI-driven cyberattacks. Threat actors use generative models to craft highly personalized phishing campaigns and automate vulnerability scanning.
To counter this, enterprises deploy defensive AI models that:
Detect AI-generated phishing patterns
Identify synthetic media manipulation
Analyze subtle behavioral deviations in user interactions
AI development Services are increasingly focused on adversarial robustness—training models to withstand manipulation attempts.
Cybersecurity is evolving into an AI-versus-AI landscape, where the most adaptive systems gain the upper hand.
Zero Trust and Continuous Verification
The Zero Trust security model has become a standard framework. It assumes that no device, user, or application is inherently trustworthy.
AI enhances Zero Trust architectures by enabling:
Continuous authentication through behavioral biometrics
Risk scoring for every access request
Real-time policy adaptation based on threat intelligence
An IoT App development company ensures that edge devices comply with Zero Trust principles through secure onboarding and device identity management.
AI development Services then layer intelligent risk assessment over every interaction, creating a continuously verified ecosystem.
Predictive Risk Modeling and Cyber Forecasting
Cyber resilience in 2026 extends beyond response—it includes prediction.
Advanced AI systems now model potential vulnerabilities based on:
Software update patterns
System configuration changes
Employee behavior analytics
External threat intelligence feeds
By simulating possible attack pathways, enterprises can proactively strengthen weak points before exploitation occurs.
Predictive modeling transforms cybersecurity from crisis management into strategic risk planning.
Regulatory Compliance and Audit Automation
Global cybersecurity regulations continue to expand, requiring transparency and accountability.
AI-powered compliance systems automate:
Continuous monitoring of regulatory controls
Automated logging and documentation
Real-time audit readiness reporting
Organizations investing in AI development Services gain automated compliance insights while reducing manual oversight burden.
Secure IoT frameworks ensure that distributed devices adhere to industry standards and data protection regulations.
Economic and Strategic Benefits of AI-Driven Cyber Resilience
AI-powered security delivers more than protection—it delivers competitive advantage.
Benefits include:
Reduced downtime from breaches
Lower incident response costs
Enhanced customer trust
Improved regulatory compliance
Stronger brand reputation
Enterprises that integrate AI development Services deeply into cybersecurity infrastructure reduce long-term risk exposure while increasing operational stability.
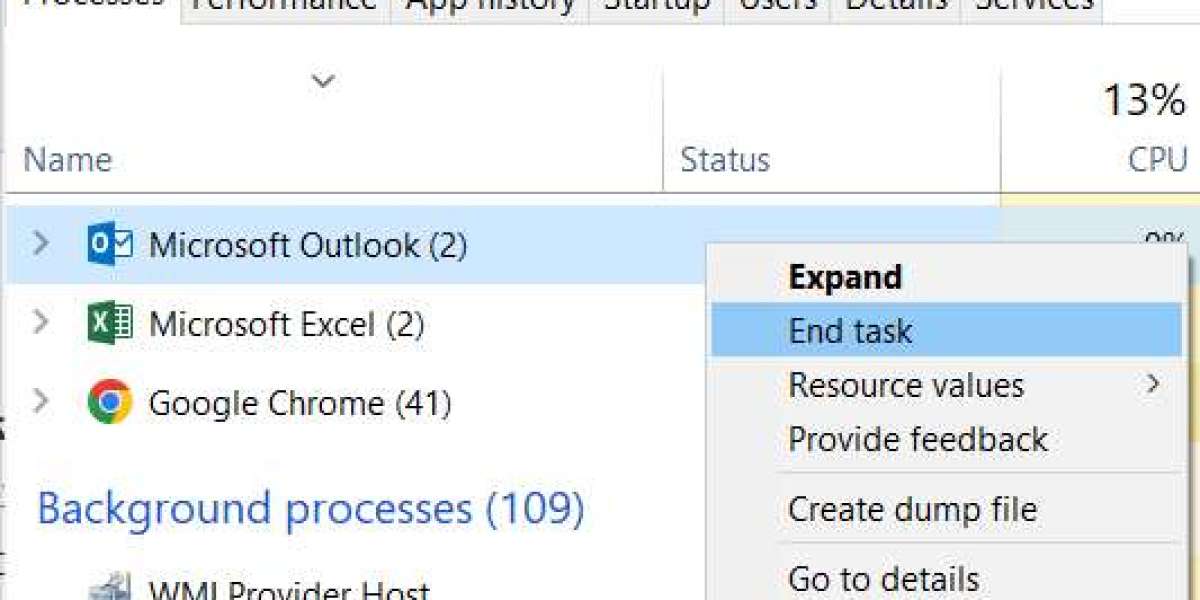
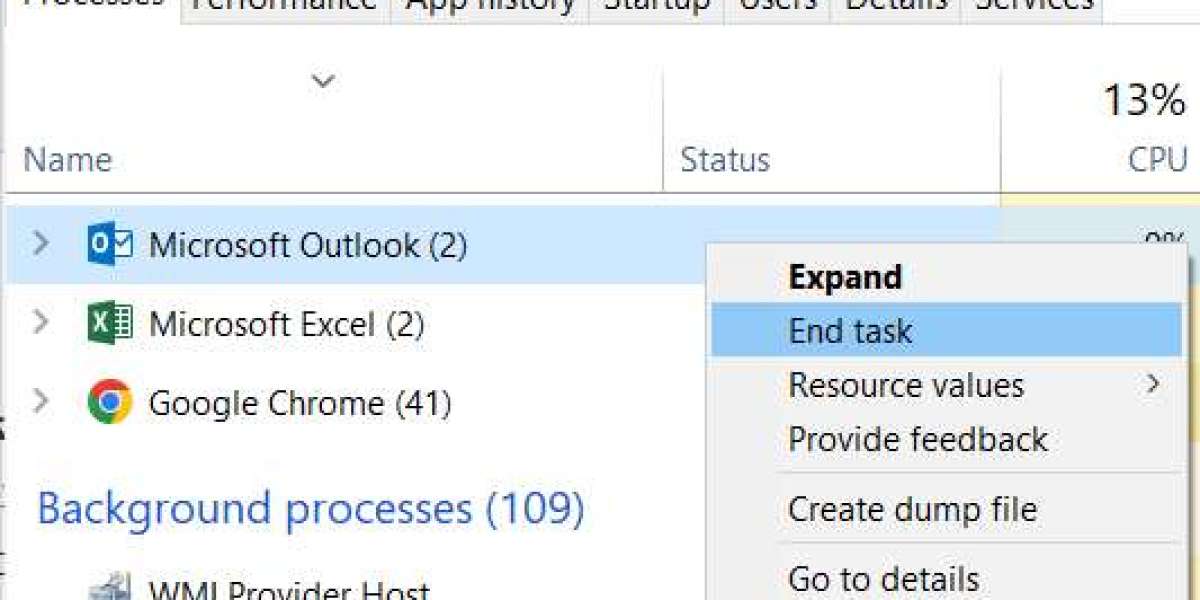
Challenges in Implementation
Building a self-defending ecosystem requires careful execution. Common challenges include:
Integrating AI into legacy security systems
Managing false positives in anomaly detection
Ensuring explainability in automated decisions
Balancing automation with human oversight
Strategic partnerships with AI specialists and an experienced IoT App development company help mitigate these risks by designing scalable, secure, and transparent systems from the outset.
Human Oversight in an Autonomous Security Framework
Despite advances in automation, human expertise remains essential.
Security teams focus on:
Interpreting complex threat intelligence
Refining AI models
Handling high-risk escalations
Ensuring ethical AI deployment
AI enhances human capability rather than replacing it.
The most resilient organizations build hybrid security teams where intelligent systems handle routine defense, and experts concentrate on strategic threat management.
Conclusion: From Defense to Digital Immunity
In 2026, cybersecurity is no longer about building walls. It is about developing digital immunity—systems capable of detecting, adapting, and healing themselves in real time.
Enterprises that invest in advanced AI development Services and collaborate with a security-focused IoT App development company are creating ecosystems that do more than resist attacks. They evolve continuously to counter them.
As cyber threats grow more intelligent, resilience must grow smarter. The organizations that thrive will be those that transform cybersecurity from a cost center into a core intelligence capability—turning risk into resilience and defense into strategic strength.