Multi-Layer Security: The Best Defense for Modern Businesses
If you are looking to protect your business from evolving cyber threats, implementing a multi-layer security strategy is no longer optional it’s essential. In 2026, businesses face increasingly sophisticated attacks ranging from ransomware and phishing to insider threats and advanced persistent threats (APTs). Relying on a single security solution is not enough to safeguard your data, systems, and reputation.
Multi-layer security, also known as defense-in-depth, provides a comprehensive approach to cybersecurity by combining multiple protective measures across different levels of your IT infrastructure. This ensures that even if one layer fails, others continue to protect your business.
What is Multi-Layer Security?
Multi-layer security is a cybersecurity strategy that uses multiple defenses to protect systems, networks, and data. Instead of relying on a single tool, it integrates various technologies, policies, and practices to create a strong security framework.
These layers typically include:
Network security
Endpoint protection
Application security
Data protection
Identity and access management
Physical security
Each layer plays a critical role in preventing, detecting, and responding to threats.
Are you searching for an It Amc Dubai UAE? Connect to Atop Computer Solution LLC.
Why Multi-Layer Security is Important in 2026
Cyber threats are becoming more complex and targeted. Attackers often exploit multiple vulnerabilities to gain access to systems. A single line of defense can be easily bypassed.
Multi-layer security helps businesses:
Reduce the risk of data breaches
Protect sensitive information
Ensure regulatory compliance
Maintain business continuity
Build customer trust
It provides a proactive approach to security, rather than reacting after an attack occurs.
Key Layers of a Multi-Layer Security Strategy
1. Perimeter Security (Network Layer)
This is the first line of defense that protects your network from external threats.
Includes:
Firewalls
Intrusion detection and prevention systems (IDS/IPS)
Secure gateways
These tools monitor incoming and outgoing traffic to block unauthorized access.
2. Endpoint Security
Endpoints such as laptops, desktops, and mobile devices are common entry points for cyberattacks.
Includes:
Antivirus and anti-malware software
Endpoint detection and response (EDR)
Device encryption
Protecting endpoints ensures that threats are stopped before they spread across the network.
3. Application Security
Applications are often targeted by attackers to exploit vulnerabilities.
Includes:
Regular software updates and patching
Secure coding practices
Web application firewalls (WAF)
This layer ensures that applications are protected against common threats such as SQL injection and cross-site scripting.
4. Data Security
Data is one of the most valuable assets of any business.
Includes:
Data encryption
Data loss prevention (DLP)
Secure backups
Protecting data ensures that even if systems are compromised, sensitive information remains secure.
5. Identity and Access Management (IAM)
Controlling who has access to your systems is critical.
Includes:
Multi-factor authentication (MFA)
Role-based access control (RBAC)
Single sign-on (SSO)
IAM ensures that only authorized users can access sensitive resources.
Are you searching for a Buy Microsoft Office 365 in UAE? Connect to Atop Computer Solution LLC.
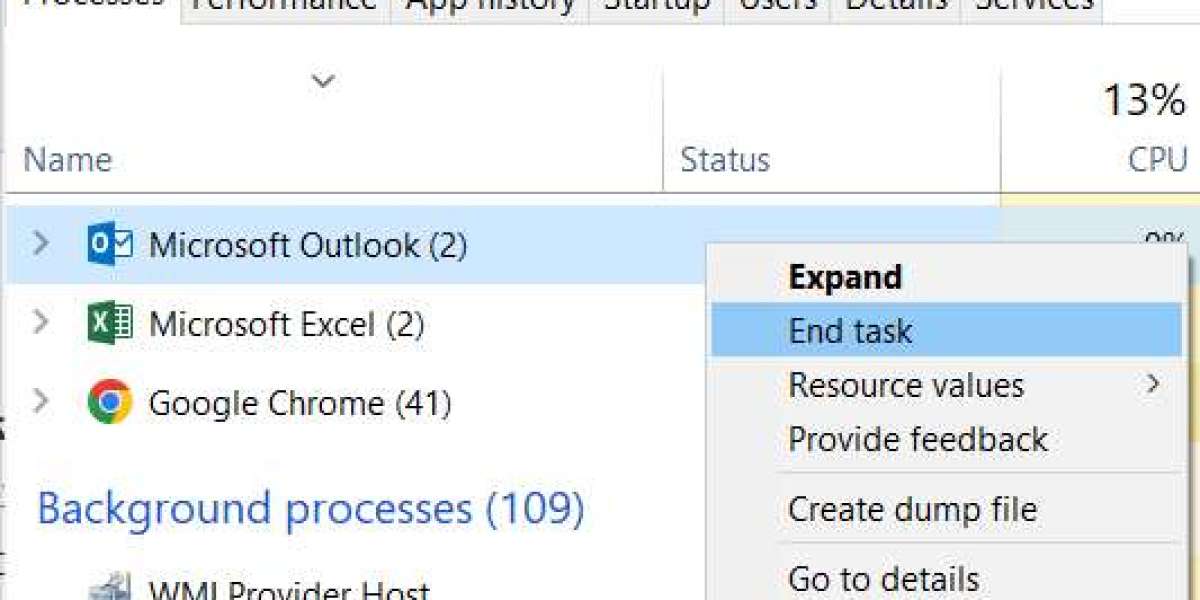
6. Monitoring and Incident Response
Continuous monitoring helps detect threats in real time.
Includes:
Security information and event management (SIEM)
Threat intelligence tools
Incident response plans
This layer enables quick detection and response to minimize damage.
7. Physical Security
Physical access to IT infrastructure must also be controlled.
Includes:
Secure server rooms
Surveillance systems
Access control systems
Physical security prevents unauthorized access to hardware and sensitive systems.
Benefits of Multi-Layer Security for Businesses
Comprehensive Protection
Multiple layers ensure that no single point of failure can compromise your entire system.
Reduced Risk of Cyberattacks
Even if attackers bypass one layer, additional defenses stop them from progressing further.
Improved Compliance
Many industries require strict security measures. Multi-layer security helps meet regulatory requirements.
Business Continuity
Strong security reduces downtime and ensures uninterrupted operations.
Enhanced Customer Trust
Customers are more likely to trust businesses that prioritize data security.
Common Cyber Threats Addressed by Multi-Layer Security
Modern businesses face a wide range of threats, including:
Ransomware attacks
Phishing and social engineering
Malware and spyware
Insider threats
Distributed Denial of Service (DDoS) attacks
A multi-layer approach ensures protection against these diverse threats.
How Atop Computer Solution LLC Strengthens Business Security
Atop Computer Solution LLC provides advanced multi-layer security solutions designed to protect businesses from modern cyber threats. With a comprehensive approach to cybersecurity, the company helps organizations build resilient and secure IT environments.
Key offerings include:
End-to-end security assessment and implementation
Advanced threat detection and prevention systems
Secure network and endpoint protection
Data encryption and backup solutions
Continuous monitoring and incident response
Customized security strategies based on business needs
By partnering with Atop Computer Solution LLC, businesses can ensure their systems are protected at every level.
Are you searching for Apple Products? Connect to Atop Computer Solution LLC.
Best Practices for Implementing Multi-Layer Security
To build an effective security strategy, businesses should:
Conduct regular security audits
Train employees on cybersecurity awareness
Keep systems updated and patched
Use strong passwords and authentication methods
Implement data backup and recovery plans
These practices strengthen each layer of your security framework.
Challenges in Implementing Multi-Layer Security
While highly effective, multi-layer security can present challenges:
Complexity in managing multiple tools
Higher initial investment
Need for skilled IT professionals
Integration between different security systems
Working with experienced providers helps overcome these challenges.
Future Trends in Cybersecurity
Cybersecurity continues to evolve as threats become more advanced. Key trends include:
AI-driven threat detection
Zero Trust security models
Cloud-based security solutions
Automation in incident response
Increased focus on data privacy regulations
Businesses that adopt these innovations will stay ahead of cyber threats.
If you are searching for IT Support Services in Dubai UAE? Connect to Atop Computer Solution LLC.
Conclusion
In today’s digital landscape, relying on a single security solution is no longer sufficient. Multi-layer security provides a comprehensive and proactive approach to protecting your business from a wide range of cyber threats.
By combining multiple defenses across network, endpoint, application, and data layers, businesses can significantly reduce risks and ensure long-term security.
With expert support from Atop Computer Solution LLC, you can implement a robust multi-layer security strategy tailored to your business needs. Investing in advanced cybersecurity measures today will safeguard your operations, protect your data, and build trust with your customers.
If you are looking to secure your business against modern threats, multi-layer security is the strongest defense you can implement.
Google Map - https://share.google/KSpp3DAFljvpkzZNo
Follow these links for more information:
https://www.acs-dxb.com/services/it-support-services-in-dubai-uae