In the modern digital world, businesses rely heavily on technology to store data, communicate with clients, and manage daily operations. While this reliance improves efficiency, it also exposes organizations to a wide range of cyber threats. As a result, understanding cyber security has become essential for businesses of all sizes.
Cyber attacks are becoming more sophisticated and frequent, targeting sensitive data such as financial information, customer details, and internal records. Without proper protection, businesses risk financial loss, reputational damage, and operational disruption. This makes cyber security a critical part of any business strategy.
By implementing strong cyber security practices, organizations can safeguard their systems and maintain trust with their customers. This article explores the key cyber security essentials every business must know to stay protected and resilient.
Understanding Cyber Security
What Is Cyber Security
Cyber security refers to the practices and technologies used to protect systems, networks, and data from cyber threats. It involves preventing unauthorized access, detecting potential risks, and responding to security incidents effectively. Businesses must adopt a comprehensive approach to ensure full protection.
Cyber security is not limited to large corporations. Small and medium sized businesses are often targeted because they may have weaker defenses. This makes it important for every organization to prioritize security measures.
A strong cyber security framework includes policies, tools, and employee awareness. Together, these elements create a secure environment that reduces the risk of cyber attacks and data breaches.
Why Cyber Security Is Important
The importance of cyber security continues to grow as businesses become more dependent on digital systems. A single security breach can lead to significant financial losses and legal consequences. Protecting sensitive data is essential for maintaining business continuity.
Cyber security also helps build trust with customers and partners. When businesses demonstrate strong security practices, they show commitment to protecting information. This enhances their reputation and credibility.
In addition, many industries require compliance with data protection regulations. Proper cyber security ensures that businesses meet these requirements and avoid penalties. It is a fundamental aspect of responsible business operations.
Common Cyber Threats Businesses Face
Malware and Ransomware
Malware is a type of malicious software designed to damage or disrupt systems. It can enter a network through infected files, emails, or websites. Once inside, it can steal data, corrupt files, or slow down operations.
Ransomware is a specific type of malware that locks access to data until a ransom is paid. This can halt business operations and cause significant losses. Cyber security measures such as antivirus software and regular updates help prevent these attacks.
Businesses should also implement backup systems to recover data in case of an attack. This reduces the impact of ransomware and ensures continuity.
Phishing Attacks
Phishing is a common cyber threat where attackers trick individuals into revealing sensitive information. This is often done through fake emails or messages that appear legitimate. Employees may unknowingly provide login details or financial information.
Cyber security training is essential to help employees recognize phishing attempts. Businesses should educate staff on identifying suspicious emails and avoiding unknown links. Awareness is a key defense against such attacks.
Implementing email filtering systems can also reduce the risk. These tools detect and block malicious messages before they reach employees.
Essential Cyber Security Practices
Strong Password Management
Passwords are the first line of defense against unauthorized access. Weak or reused passwords can make systems vulnerable to attacks. Businesses must enforce strong password policies to enhance cyber security.
Employees should use complex passwords that include a combination of letters, numbers, and symbols. Regular password updates are also important to maintain security. Multi factor authentication adds an extra layer of protection.
Password management tools can help store and manage credentials securely. These tools reduce the risk of password related breaches and improve overall security.
Regular Software Updates
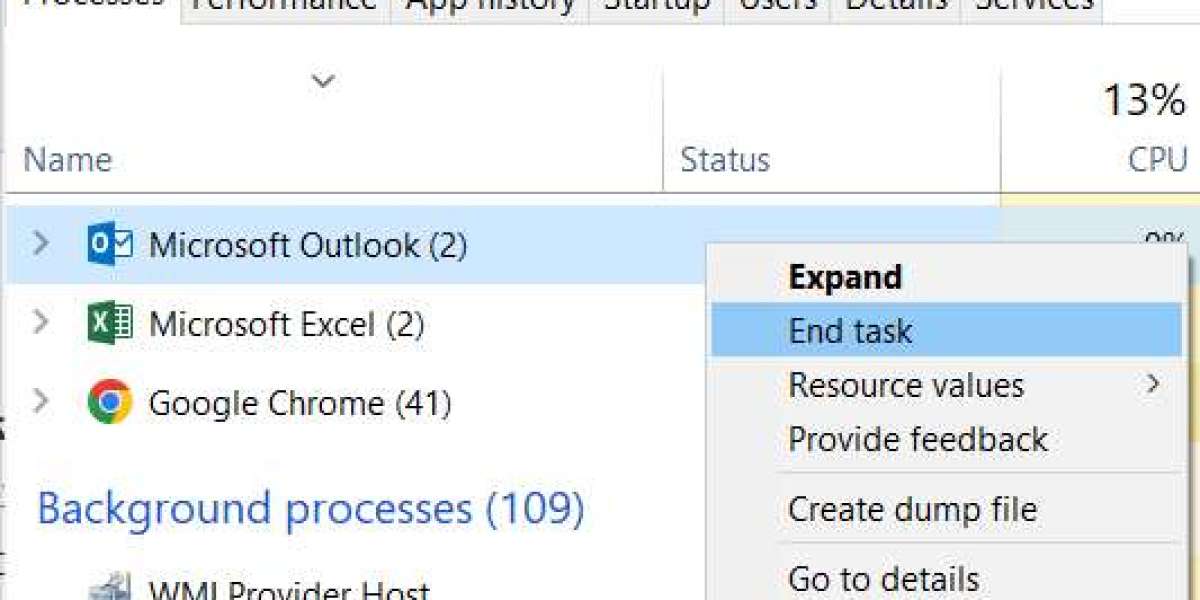
Keeping software up to date is a crucial aspect of cyber security. Updates often include patches that fix vulnerabilities and improve performance. Outdated systems are more susceptible to attacks.
Businesses should ensure that all software, including operating systems and applications, is updated regularly. Automated updates can help maintain consistency and reduce the risk of oversight.
Regular updates also improve system efficiency and compatibility. This contributes to both security and productivity.
Network Security Measures
Firewalls and Intrusion Detection
Firewalls act as a barrier between internal networks and external threats. They monitor incoming and outgoing traffic to prevent unauthorized access. This is a fundamental component of cyber security.
Intrusion detection systems identify suspicious activity within the network. These systems alert administrators to potential threats, allowing for quick response. Together, these tools enhance overall security.
Businesses should configure firewalls and detection systems properly to ensure effectiveness. Regular monitoring helps maintain a secure network environment.
Secure Wi Fi Networks
Unsecured wireless networks can be an easy target for cyber attackers. Businesses must ensure that their Wi Fi networks are protected with strong encryption. This prevents unauthorized access to sensitive data.
Changing default router settings and using strong passwords are important steps. Network segmentation can also improve security by separating critical systems from general access.
Secure Wi Fi practices are essential for protecting business operations. They help prevent data breaches and maintain system integrity.
Data Protection and Backup
Importance of Data Encryption
Encryption is a key aspect of cyber security that protects data by converting it into unreadable formats. Only authorized users with the correct keys can access the information. This ensures that sensitive data remains secure.
Businesses should use encryption for both stored data and data in transit. This protects information from interception and unauthorized access. Encryption is especially important for financial and personal data.
Implementing encryption enhances security and supports compliance with regulations. It is a critical tool for data protection.
Regular Data Backups
Data backups are essential for recovering information in case of cyber attacks or system failures. Businesses should implement regular backup schedules to ensure data is always protected.
Backups should be stored in secure locations, including offsite or cloud storage. This prevents loss in case of physical damage or cyber incidents. Testing backups regularly ensures they can be restored when needed.
Having reliable backups reduces downtime and supports business continuity. It is a vital component of any cyber security strategy.
Employee Training and Awareness
Building a Security Conscious Culture
Employees play a crucial role in maintaining cyber security. Human error is one of the leading causes of security breaches. Businesses must create a culture where security is a shared responsibility.
Training programs should educate employees on best practices and potential threats. This includes recognizing phishing attempts, using secure passwords, and following company policies.
A security conscious workforce helps reduce risks and improve overall protection. Awareness is a powerful tool in preventing cyber attacks.
Establishing Clear Security Policies
Clear policies provide guidelines for maintaining cyber security within an organization. These policies should outline acceptable use of systems, data handling procedures, and response protocols.
Employees should be familiar with these policies and understand their responsibilities. Regular updates ensure that policies remain relevant to current threats.
Enforcing security policies helps maintain consistency and accountability. This strengthens the organization’s overall security framework.
Incident Response and Recovery
Preparing for Cyber Incidents
Despite best efforts, cyber incidents can still occur. Businesses must have a plan in place to respond quickly and effectively. An incident response plan outlines the steps to take in case of a breach.
This includes identifying the issue, containing the threat, and minimizing damage. Quick action helps reduce the impact on operations and data.
Regular testing of the response plan ensures readiness. Preparedness is essential for managing cyber risks.
Learning from Security Incidents
After a cyber incident, it is important to analyze what happened and identify areas for improvement. This helps prevent similar incidents in the future. Businesses should conduct thorough reviews and update their security measures.
Learning from incidents strengthens the overall cyber security strategy. It allows organizations to adapt to evolving threats.
Continuous improvement ensures that businesses remain protected in a changing environment. This proactive approach supports long term security.
Conclusion
Cyber security is an essential part of modern business operations. By understanding common threats and implementing effective practices, organizations can protect their systems, data, and reputation. From strong passwords and regular updates to employee training and incident response, each element plays a vital role in maintaining security.
Businesses that prioritize cyber security are better equipped to handle risks and maintain trust with their customers. A proactive approach ensures resilience and long term success in a digital world.
For organizations looking to strengthen their cyber security strategy, Hubtel IT provides reliable solutions and expert support to help businesses stay protected and prepared for evolving threats.